📚 VirusTotal += Mandiant Permhash: Unearthing adversary infrastructure and toolkits by leveraging permissions similarity
💡 Newskategorie: Malware / Trojaner / Viren
🔗 Quelle: blog.virustotal.com
Last Monday our colleagues over at Mandiant rolled out Permhash. In their own words, Permhash is an extensible framework to hash the declared permissions applied to Chromium-based browser extensions and APKs allowing for clustering, hunting, and pivoting similar to import hashing and rich header hashing. We are excited to announce that we have been working closely with Jared Wilson on the Mandiant side to support Permhash similarity pivoting in VirusTotal.
VirusTotal already supports multiple similarity pivots: vhash (VirusTotal’s home-grown static feature hash), behash (same concept but for dynamic analyses), ssdeep, imphash, TLSH, telfhash, main icon dhash, etc. We have blogged extensively in the past about how similarity can be used to expand context and map out threat campaigns, we even hosted a joint webinar with Trend Micro and Trinity Cyber on this very topic. But let’s see how Permhash builds upon VirusTotal’s threat hunting swissknife and provides yet another orthogonal vehicle to track threat actors and their toolkits, going beyond IoCs and rather focusing on repeatable toolkit patterns.
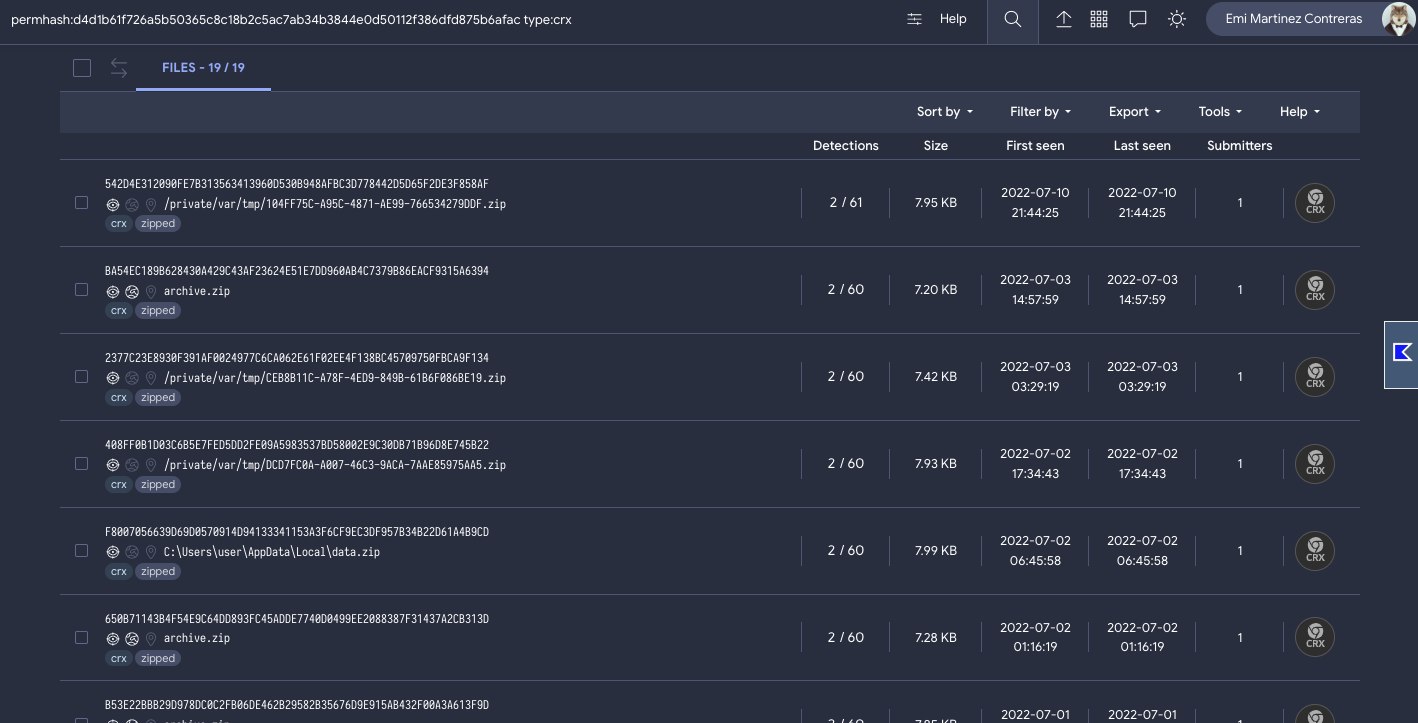
In their article, Mandiant writes about UNC3559 and CHROMELOADER. UNC3559 is a financially motivated threat cluster that has distributed the CHROMELOADER dropper since at least early 2022. CHROMELOADER is a dropper that subsequently downloads a malicious Chrome extension, which can display advertisements in the browser and capture browser search data. Mandiant shares a particular CHROMELOADER manifest, you can use that initial input to pivot to other similar files via Permhash, and you can combine it with other search modifiers to narrow down results to actual Chrome Extensions as opposed to manifests:permhash:d4d1b61f726a5b50365c8c18b2c5ac7ab34b3844e0d50112f386dfd875b6afac type:crx
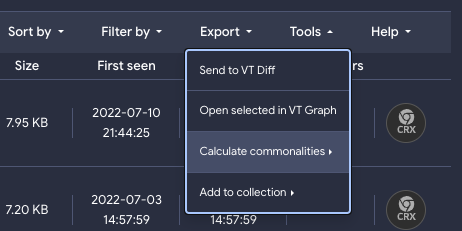
With a single click we get to 19 other potential variations by the same threat group, many of them with low detection coverage by the industry (we are starting to get proactive):
Indeed, the execution parents tell us about those files that when detonated in our sandboxes drop the Chrome extensions under study. That’s how we can learn that the first stage malware consists of both DMG files (6 files, example) and Powershell scripts/commands (3 files, example):
By the way, VirusTotal Code Insight comes in very handy in understanding the 3 powershell scripts that drop Chromeloader (see for yourself):
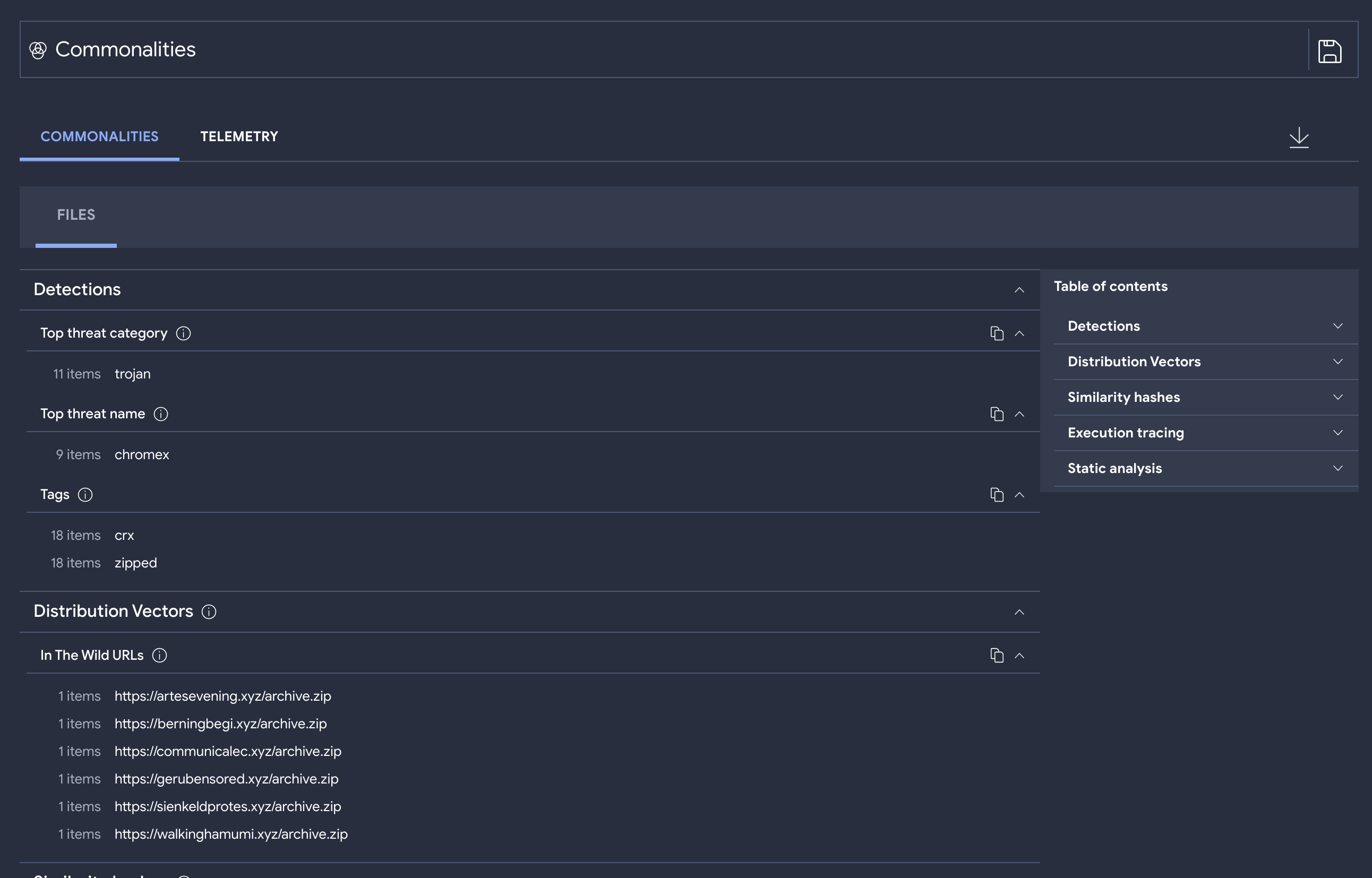
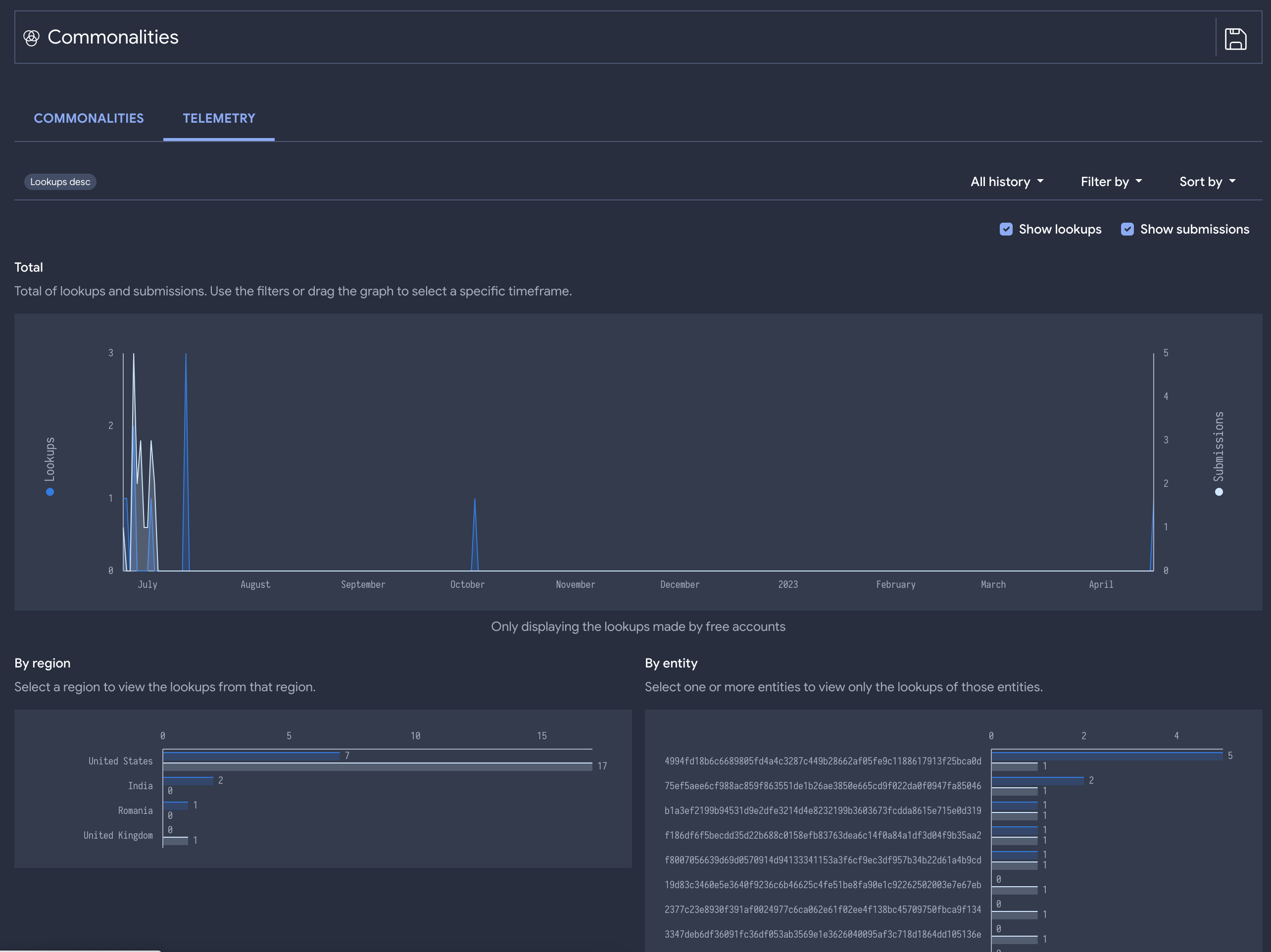
By iteratively calculating the commonalities of the first stage malware we can identify other repeatable patterns to detect these campaigns and even understand when and where has this group been active based on crowdsourced telemetry gathered from VirusTotal’s open community:
It seems to have been a relatively targeted campaign mostly targeting US orgs and active during July 2022.
Moreover, now that we have a group of variants as opposed to a single instance, we can study those files or even leverage tools like VTDIFF to build a YARA rule that can be used to hunt within our environment or to track relevant adversaries going forward in time (Livehunt) and take proactive actions as they evolve.
Oh, and one more thing, stay tuned because we will soon provide consolidated similarity searching across all similarity pivots taking into account prevalence and overlaps to identify best matches without having to search for each different similarity vector (vhash, ssdeep, permhash, imphash, etc.).
Happy hunting!


 800+ IT
News
als RSS Feed abonnieren
800+ IT
News
als RSS Feed abonnieren