📚 Tango down report of OP China ELF DDoS'er
💡 Newskategorie: Malware / Trojaner / Viren
🔗 Quelle: blog.malwaremustdie.org
This report is credited to the team work between MMD, CERT and fellow researchers involved.
Tango OP Announcement:
We are releasing the take-down (Tango OP) project information of our current on-going operation against the ELF DDoS malware, the threat with origin from China.
The threat is verdicted to be originated from China based on:
1. The source binary data contains China specific details
2. Attacker IP address during attempt to infect are mostly (98%) originated from China network
3. Panels served by ELF malware be downloaded during infection, are located in China network (98%)
4. CNC server used for downloading config or used for remote attack (92%)
The distributed malware are separated into 3 categories:
1. "Elknot" variants, technical information: --> [link]
2. "AES.DDoS", technical information: --> [link]
3. ".IptabLes|x", technical information: --> [link]
4. "BillGates", technical information: --> [link]
5. (NEW) "GoARM.Bot", technical information: --> [link]
6. "XOR.DDoS", technical information: --> [link]
The malware analyzed was compiled with aiming NIX base routers/servers, with these OS & CPU architectures:
1. Intel x32 (Linux / FreeBSD)
2. Intel x64 (Linux / FreeBSD)
3. AMD x64 (Linux)
3. ARM (Linux)
4. MIPS (Linux)
5. (NEW) PPC (Linux)
(NEW) The Windows version of the same DDoSer was started to be detected in Mid October 2014.
Samples: [-1-] [-2-]
PoC, Evidence & Samples
We have some video recorded as hard evidence of the attack in progress as per listed in the links below:
1. https://www.youtube.com/watch?v=JjtOUto9Sr8
2. https://www.youtube.com/watch?v=z6MdtFck6x4
3. https://www.youtube.com/watch?v=sdKCjbrs5uQ
4. https://www.youtube.com/watch?v=YtxaT1rahY8
5. https://www.youtube.com/watch?v=OcOiuxAtbOk
We also posted three awareness , for the detail analysis of this threat:
1. May 2014 [link]
2. June 2014 [link]
3. Sept 2014 [link]
View of some download panel video & pictures for evidence:





Thank you @300trg for fixing the 5th picture↑
Video as PoC of the many alive panels exists:
Video as PoC of how DDoS ELF malware placed in their "panels" are downloaded during an ssh hacked session of a NIX OS base machine:
Illustration of "Volume & Combination" in its distribution
In a panel served with ELF malware, China DDoS'er crooks is distributing quite big amount of downloads (even we are assuming 70% downloads are for infection), as per seen in one panel snapshot picture below: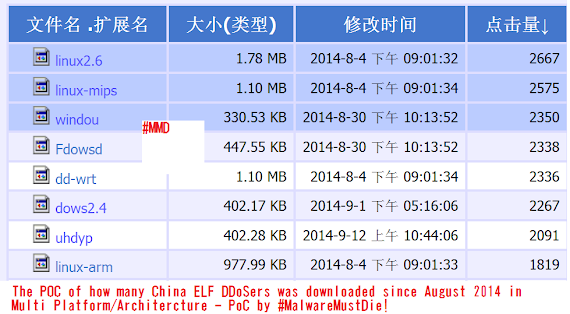
In a panel we often spotted the China crook is mixing the type of malware, as per seen in the PoC below:
Mixing samples PoC:↓
Recent ELF samples we collected & analyzed for the past one month:
(there are a lot more than these..and these are still coming)
https://www.virustotal.com/en/file/276b2bb1bb19e7b81e7656a6c411a094952592f77948151d43d460907e9702de/analysis/
https://www.virustotal.com/en/file/cb4aa1bc0a65771b7a23afc99d559a9943ebe06901b6ba37fcf563c64f28a872/analysis/
https://www.virustotal.com/en/file/586c2afdedef5e2ff0298b6bb5d8e11d847d35e86b2be56b437a35227643fb58/analysis/
https://www.virustotal.com/en/file/bfdad0437c12ccfb2b5406f902bcae0856c716a6f8b6c3b5e925a48e12ca51ec/analysis/
https://www.virustotal.com/en/file/afece0410779068b43c122008dad83af98a6a20e37f4414a99587ebc0f9f13d1/analysis/
https://www.virustotal.com/en/file/daccf72b00939ef0f14eb19b2a9cf73a61514a4c86d28369886634644fb0159d/analysis/
https://www.virustotal.com/en/file/77100c8e3ec940af6336bf5a8772057ed1a052658f0af5e6bb4a0f853ebb7a82/analysis/
https://www.virustotal.com/en/file/9d43b31bc47a4fff65ab5156e2fc348bf36451d58d00850a1f3c21e2d696910b/analysis/
https://www.virustotal.com/en/file/e27571a89dfbb256bdf2aa7ff0a062bd10bd712c46d7ddc045a8ac85c4903c2f/analysis/
https://www.virustotal.com/en/file/c1014f0ff0efc018e28300c2296459948489bd5d22633a0af1ca6ffb0c2336fe/analysis/
https://www.virustotal.com/en/file/3f50c0f70e3eb2debf77ba7626e9c358d7ed02d57ee6da375c0b507006df3da5/analysis/
https://www.virustotal.com/en/file/393ac47184475af099eafce91d7472ea5af1d74636a992cc08bf40872d22fa4a/analysis/
https://www.virustotal.com/en/file/3f50c0f70e3eb2debf77ba7626e9c358d7ed02d57ee6da375c0b507006df3da5/analysis/
https://www.virustotal.com/en/file/393ac47184475af099eafce91d7472ea5af1d74636a992cc08bf40872d22fa4a/analysis/
https://www.virustotal.com/en/file/b81cc1f3d87fe5eddb8dec8140f0f255697a58284882d9edc4e8d636b75772c3/analysis/
https://www.virustotal.com/en/file/6dd946e821df59705dcfeb79fab810336d0ee497fd715fb5b6711e05c0428f4d/analysis/
https://www.virustotal.com/en/file/9746054219bfa20e0bf55a066acd447a8878913d4b857057729a579cb1a078b3/analysis/
https://www.virustotal.com/en/file/8fa44a7b3eb707f584b223792bdb78b1e5f69a40dba20634094077c2f0287bca/analysis/
https://www.virustotal.com/en/file/d2b3ce2195b1422c165faeb1fbbdd098f13df6cf6595fb18f8d618cd78df597c/analysis/
https://www.virustotal.com/en/file/bb4786695774ae7777200a78e56db83ad5d5bdf1c1b84ef86dd796f7c9a3e1b4/analysis/
https://www.virustotal.com/en/file/406074b1c168602163a8c246f88ae9914f54ceacc47ec7fa0d8d3116e35374be/analysis/
https://www.virustotal.com/en/file/393ea466d635ea97150ca4bc52b6de7c47da2e7bffae28248b388523141a1cc8/analysis/
https://www.virustotal.com/en/file/470dbcc291008e183e46a81ce84aff1f90131f5a3d1fb30caf885769748d981e/analysis/
https://www.virustotal.com/en/file/661233de0cd229dbcbe37c06c2a6c86e1dbc081072e03c3207c00c6ce19aa57c/analysis/
https://www.virustotal.com/en/file/96aad20e56a59389117609aa192fc1771e105741e2e04664de56ecc1545a4c8a/analysis/
https://www.virustotal.com/en/file/223f66e52e84cfa21ae94053152e015f652894f77d129b3b738bb4937cfc857d/analysis/
https://www.virustotal.com/en/file/701ea25c01212e6f21ffbf5e60214a441558825ec9b86159e19b1f9576962e86/analysis/
https://www.virustotal.com/en/file/0383b323737e02f2e39a9ade6539432f7bb17ebb79fd809510a8ea1102963a0d/analysis/
https://www.virustotal.com/en/file/18ee96df892b632073d1d6ecc3c339dd120e66411c15eff176efcf2c1728cfc7/analysis/
https://www.virustotal.com/en/file/dc2b6a4d1e1f4014f0f9c3fb13908a3f46f9cb6a01a51f6447f9e85d3d1abcfe/analysis/
https://www.virustotal.com/en/file/5e3aea8e7f297685ddca0fadf9503d350d78be6f0bca700dc79fccc2ac9f925d/analysis/
https://www.virustotal.com/en/file/f5e7ba8d7b40415c7cbb8f45177deb5daffc2450c9f64d0e5c2ed65b9d9d7d55/analysis/
https://www.virustotal.com/en/file/d86a12974631e8711b9bce8fdf1f1fd4775f741461274005b2362647f17a63c6/analysis/
[..]
Tango down result so far of the China ELF DDoS'er download panels:
'h00p:/222.76. 210.140:81
h00p://122.94. 40.23:38384
h00p://60.173. 10.184:8080
h00p://122.142. 161.163:8080
h00p://125.46. 53.155:1996
h00p://183.60. 197.240:8181
h00p://112.117. 223.10:280
h00p://23.95.28. 228:8080
h00p://61.164. 145.100:89
h00p://108.171. 200.16:3100
h00p://183.56. 173.44:281
h00p://112.117. 223.10:789
h00p://61.147. 103.21:8080
h00p://218.25. 36.220:630
h00p://183.60. 197.240:8181
h00p://120.210. 204.102:999
h00p://174. 139.20.66:10080/
h00p://119. 90.135.206/
h00p://183. 60.142.173:523
h00p://183. 60.149.199:8081
h00p://183. 60.202.61:8088
h00p://183. 56.173.44:281
h00p://162. 221.12.193:68
h00p://218. 28.116.248
h00p://108. 171. 200.16:3100
h00p://183.60. 197.240:8181
h00p://199.192. 158.36:888
h00p://218.6.12. 157:8023
h00p://182.254. 168.157:4343
h00p://110.80. 129.134:999/
h00p://183.60. 202.91:2013/
h00p://182.254. 168.157:4343/
h00p://182. 254.180.241:2015/
h00p://219. 235.8.29:2015/
h00p://104.194.6.138:110/
h00p://121.127.241.55:8081/
h00p://183. 60.202.209:44435/
h00p://218.84. 198.37:10042/
h00p://114.215. 140.230:55/1231
h00p://183.60. 109.78:45852/
h00p://222. 186.30.239:999/
h00p://61. 36.33.225:81/
h00p://115. 29.165.174:38886/
h00p://111. 73.45.198:5888/
h00p://121. 40.85.20:8686/
h00p://199. 83.94.82:1991/
h00p://222. 186.34.152/
h00p://121. 42.12.57:8081/
h00p://117. 41.229.139:24/
h00p://119. 97.184.42:9999/
h00p://192. 169.219.22:280/
h00p://222. 186.56.33:33123/
h00p://118. 123.119.14 :4743/
h00p://115. 28.6.74 :8084/
h00p://23. 245.205.38 :8452/
h00p://119. 97.184.42 :9999/
h00p://a1285858501.f3322.org:8889/ 'OP Chopsticks'
h00p://192.169.219.22:280/
h00p://222.186.42.31:7019/
h00p://183.136.214.14:12345/
h00p://183.60.202.58:5147/
h00p://124.173.118.167:41235/
h00p://222.186.58.146:81/
h00p://183.60.202.58:5147/
h00p://222.186.58.146:81/
h00p://118.123.119.14:3543/
h00p://116.255.162.80:3322/
h00p://104.194.25.172/
h00p://218.244.148.150:24/
h00p://104.194.25.176:8080/
h00p://www.qiuwo.net/
h00p://www11359ui.sakura.ne.jp/
h00p://104.194.11.72:8080/
h00p://222.186.34.210:5487/
h00p://222.186.34.123:123/
h00p://118.244.150.49:8889/
h00p://58.53.128.71:4567/
h00p://221.194.44.197:8080/
h00p://183.60.149.194:801/
h00p://58.53.128.71:4567/
h00p://60.173.9.144:8088/
h00p://60.173.9.43:8088/
h00p://199.168.100.72:831/
h00p://125.93.53.218:8888/
h00p://123.249.33.21:1996/ '
Detail network information for the origin of ELF malware panel addresses above:
222.76.210.140||4134 | 222.76.0.0/14 | CHINANET | CN | - | XIAMEN TELECOM IDC
122.94.40.23||9394 | 122.94.0.0/16 | CTTNET | CN | CHINATIETONG.COM | CHINA TIETONG TELECOMMUNICATIONS CORPORATION
60.173.10.184||4134 | 60.168.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET ANHUI PROVINCE NETWORK
122.142.161.163|163.161.142.122.adsl-pool.jlccptt.net.cn.|4837 | 122.136.0.0/13 | CHINA169 | CN | CHINAUNICOM.COM | CHINA UNICOM JILIN PROVINCE NETWORK
125.46.53.155|hn.kd.ny.adsl.|4837 | 125.40.0.0/13 | CHINA169 | CN | CHINAUNICOM.COM | CHINA UNICOM HENAN PROVINCE NETWORK
183.60.197.240||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
112.117.223.10|10.223.117.112.broad.km.yn.dynamic.163data.com.cn.|4134 | 112.116.0.0/15 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET YUNNAN PROVINCE NETWORK
23.95.28.228|host.colocrossing.com.|36352 | 23.95.24.0/21 | AS-COLOCROSSING | US | HUDSONVALLEYHOST.COM | HUDSON VALLEY HOST
61.164.145.100||4134 | 61.164.0.0/16 | CHINANET | CN | - | WENZHOU TELECOM CO. LTD
108.171.200.16|108-171-200-16.static.webnx.com.|18450 | 108.171.192.0/19 | WEBNX | US | WEBNX.COM | WEBNX INC.
183.56.173.44||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
112.117.223.10|10.223.117.112.broad.km.yn.dynamic.163data.com.cn.|4134 | 112.116.0.0/15 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET YUNNAN PROVINCE NETWORK
61.147.103.21||65222 | 61.147.103.21/32 | -Private | | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
218.25.36.220||4837 | 218.25.0.0/16 | CHINA169 | CN | CHINAUNICOM.COM | CHINA UNICOM LIAONING PROVINCE NETWORK
183.60.197.240||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
120.210.204.102||9808 | 120.210.192.0/19 | CMNET | CN | CHINAMOBILELTD.COM | CHINA MOBILE COMMUNICATIONS CORPORATION
174.139.20.66|customer.krypt.com.|35908 | 174.139.20.0/24 | VPLSNET | US | KRYPT.COM | KRYPT TECHNOLOGIES
119.90.135.206||23724 | 119.90.128.0/17 | CHINANET-IDC-BJ | CN | CNPC.COM.CN | HUABEI OIL FIELD COMMUNICATION CO
183.60.142.173||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
183.60.149.199||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
183.60.202.61||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
183.56.173.44||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
162.221.12.193|193.12.221.162.clear-ddos.com.|62466 | 162.221.12.0/24 | CLEAR-DDOS-AS | CA | CLEAR-DDOS.COM | CLEARDDOS TECHNOLOGIES
218.28.116.248|pc0.zz.ha.cn.|4837 | 218.28.0.0/15 | CHINA169 | CN | CHINAUNICOM.COM | CHINA UNICOM HENAN PROVINCE NETWORK
108.171.200.16|108-171-200-16.static.webnx.com.|18450 | 108.171.192.0/19 | WEBNX | US | WEBNX.COM | WEBNX INC.
183.60.197.240||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
199.192.158.36||6939 | 199.192.152.0/21 | HURRICANE | US | EHOSTINGUSA.COM | VPS21 LTD
218.6.12.157||4134 | 218.6.0.0/17 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET FUJIAN PROVINCE NETWORK
182.254.168.157||45090 | 182.254.168.0/23 | CNNIC-TENCENT-NET | | - | COMSENZ TECHNOLOGY LTD
183.60.202.91||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
110.80.129.134||4134 | 110.80.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET FUJIAN PROVINCE NETWORK
182.254.168.157||45090 | 182.254.168.0/23 | CNNIC-TENCENT-NET | | - | COMSENZ TECHNOLOGY LTD
182.254.180.241||45090 | 182.254.180.0/23 | CNNIC-TENCENT-NET | | - | COMSENZ TECHNOLOGY LTD
219.235.8.29|host-219-235-8-29.iphost.gotonets.com.|17621 | 219.235.8.0/24 | CNCGROUP | CN | GOTONETS.COM | SHANGHAI QIANWAN NETWORK CO. LTD
104.194.6.138||36114 | 104.194.0.0/19 | VWEB-8 | US | VERSA14 | VERSAWEB, LLC
121.127.241.55||38197 | 121.127.241.0/24 | SUNHK-DATA-AS | HK | SUN.NET.HK | SUN NETWORK (HONG KONG) LIMITED
183.60.202.209||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
218.84.198.37||4134 | 218.84.0.0/16 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET XINJIANG PROVINCE NETWORK
114.215.140.230||37963 | 114.215.0.0/16 | CNNIC-ALIBABA-CN-NET | CN | ALIYUN.COM | ALIYUN COMPUTING CO. LTD
183.60.109.78||65222 | 183.60.109.78/32 | -Private | | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
222.186.30.239||23650 | 222.186.30.0/24 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
61.36.33.225||3786 | 61.32.0.0/13 | LGDACOM | KR | DA-COM.COM | DACOM CORP.
115.29.165.174||37963 | 115.29.0.0/16 | CNNIC-ALIBABA-CN-NET | CN | ALIYUN.COM | ALIYUN COMPUTING CO. LTD
111.73.45.198||4134 | 111.72.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET JIANGXI PROVINCE NETWORK
121.40.85.20||37963 | 121.40.0.0/14 | CNNIC-ALIBABA-CN-NET | CN | ALIYUN.COM | ALIYUN COMPUTING CO. LTD
199.83.94.82|unassigned.psychz.net.|40676 | 199.83.88.0/21 | AS40676 | US | PSYCHZ.NET | PSYCHZ NETWORKS
222.186.34.152||23650 | 222.186.34.0/23 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
121.42.12.57||37963 | 121.42.0.0/18 | CNNIC-ALIBABA-CN-NET | CN | ALIYUN.COM | ALIYUN COMPUTING CO. LTD
117.41.229.139||4134 | 117.40.0.0/14 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET JIANGXI PROVINCE NETWORK
119.97.184.42|42.184.97.119.broad.wh.hb.dynamic.163data.com.cn.|4134 | 119.96.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET HUBEI PROVINCE NETWORK
192.169.219.22|ip-192-169-219-22.ip.secureserver.net.|26496 | 192.169.216.0/22 | AS-26496-GO-DADDY-CO | US | GODADDY.COM | GODADDY.COM LLC
222.186.56.33||23650 | 222.186.56.0/21 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
118.123.119.14||38283 | 118.123.119.0/24 | CHINANET-SCIDC-AS | CN | CHINATELECOM.COM.CN | CHINANET SICHUAN PROVINCE NETWORK
115.28.6.74||37963 | 115.28.0.0/16 | CNNIC-ALIBABA-CN-NET | CN | ALIYUN.COM | ALIYUN COMPUTING CO. LTD
23.245.205.38|38.205-245-23.rdns.scalabledns.com.|18978 | 23.244.0.0/15 | ENZUINC-US | US | ENZU.COM | ENZU INC
119.97.184.42|42.184.97.119.broad.wh.hb.dynamic.163data.com.cn.|4134 | 119.96.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET HUBEI PROVINCE NETWORK
222.186.50.229||23650 | 222.186.50.0/23 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
192.169.219.22|ip-192-169-219-22.ip.secureserver.net.|26496 | 192.169.216.0/22 | AS-26496-GO-DADDY-CO | US | GODADDY.COM | GODADDY.COM LLC
222.186.42.31||65222 | 222.186.42.31/32 | -Private | | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
183.136.214.14||4134 | 183.128.0.0/11 | CHINANET | CN | DKW.COM.CN | NINBO LANZHONG NETWORK LTD
183.60.202.58||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
124.173.118.167||4134 | 124.172.0.0/15 | CHINANET | CN | SZGWBN.NET.CN | WORLD CROSSING TELECOM (GUANGZHOU) LTD.
222.186.58.146||23650 | 222.186.56.0/21 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
183.60.202.58||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
222.186.58.146||23650 | 222.186.56.0/21 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
118.123.119.14||38283 | 118.123.119.0/24 | CHINANET-SCIDC-AS | CN | CHINATELECOM.COM.CN | CHINANET SICHUAN PROVINCE NETWORK
116.255.162.80||37943 | 116.255.128.0/17 | CNNIC | CN | - | ZHENGZHOU GIANT COMPUTER NETWORK TECHNOLOGY CO. LTD
104.194.25.172||36114 | 104.194.0.0/19 | VERSAWEB-ASN | US | VERSAWEB.COM | VERSAWEB LLC
218.244.148.150||37963 | 218.244.128.0/19 | CNNIC-ALIBABA-CN-NET | CN | - | HICHINA TELECOM NET
104.194.25.176||36114 | 104.194.0.0/19 | VERSAWEB-ASN | US | VERSAWEB.COM | VERSAWEB LLC
23.27.192.115||18779 | 23.27.192.0/20 | EGIHOSTING | US | EGIHOSTING.COM | EGIHOSTING
133.242.161.133|www11359ui.sakura.ne.jp.|7684 | 133.242.0.0/16 | SAKURA | JP | SAKURA.AD.JP | SAKURA INTERNET INC.
104.194.11.72|104-194-\$11.unassigned.userdns.com.|36114 | 104.194.0.0/19 | VERSAWEB-ASN | US | VERSAWEB.COM | VERSAWEB LLC
222.186.34.210||23650 | 222.186.34.0/23 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
222.186.34.123||23650 | 222.186.34.0/23 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK
118.244.150.49||4847 | 118.244.128.0/19 | CNIX | CN | BISS.COM.CN | BEIJING TONGHUI NETLINK DATA TECHNOLOGY CO. LTD
58.53.128.71||4134 | 58.48.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET HUBEI PROVINCE NETWORK
221.194.44.197||4837 | 221.194.0.0/16 | CHINA169 | CN | CHINAUNICOM.COM | CHINA UNICOM HEBEI PROVINCE NETWORK
183.60.149.194||4134 | 183.0.0.0/10 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
58.53.128.71||4134 | 58.48.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET HUBEI PROVINCE NETWORK
60.173.9.144||4134 | 60.168.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET ANHUI PROVINCE NETWORK
60.173.9.43||4134 | 60.168.0.0/13 | CHINANET | CN | CHINATELECOM.COM.CN | CHINANET ANHUI PROVINCE NETWORK
199.168.100.72||33387 | 199.168.96.0/21 | DATASHACK | US | DATASHACK.NET | DATASHACK LC
125.93.53.218||65222 | 125.93.53.218/32 | -Private | | CHINATELECOM.COM.CN | CHINANET GUANGDONG PROVINCE NETWORK
123.249.33.21||4134 | 123.249.0.0/17 | CHINANET | CN | CDNZZ.NET | WONTEN NETWORK LTD.
Below is the list of IP addresses to block (Tango Queue List)
(N/A)
Statistic of historical IP distribution
Please click the picture below to see Google Map statistic data:
For the better geographical view of the CNC/panel distribution please use this map: https://batchgeo.com/map/d4c4950afd0f6fb5a6ea0e6d036c0df3 thank's @malm0use!
We thank all entities who are kindly helping us to fight this threat. We look forward to keep on having good coordination to take down more infector IP addresses and domains.
If you happened to have ELF malware, please do not hesitate to send us sample by uploading to this-->[link] URL.
Please help our effort to report us the existence of new panels if the IP is not on the above lists (Tango or Queue List), by writing the comment under this post (will not be published), or mention to @malwaremustdie (twitter).
Comment & follow up:
Preliminary stage of takedown (was only 11 confirmed that time)
There's NO bullet proof anymore but there's only laziness.
We #TANGO'ed 11 #China #ELF #DDoS #CNC
#MalwareMustDie! pic.twitter.com/qbVvib16pN
— MalwareMustDie, NPO (@MalwareMustDie) September 14, 2014What is the impact of this take down to the actor(s) actually?
.@lvdeijk this takedown will hurt the crooks badly, since every CNC need to be decoded in #ELF binary, they cry hard. And they deserve it.
— MalwareMustDie, NPO (@MalwareMustDie) September 14, 2014Follow up (the next takedown):
Three more taken down, total China #ELF #malware #tango = 32 panels
Updated: http://t.co/n2gKTXSDDh
#MalwareMustDie pic.twitter.com/026fb4dDiL
— MalwareMustDie, NPO (@MalwareMustDie) September 18, 2014Just confirmed #Tango on #China #ELF #malware panels, 6 more went down (pic) - Will add this to blog.
#MalwareMustDie pic.twitter.com/GaP2Exthcf
— MalwareMustDie, NPO (@MalwareMustDie) September 20, 20143 panels #ELF #China #DDoS'er was nuked (pic).
#Tango now: 40 + 4 more to go http://t.co/n2gKTXSDDh
#MalwareMustDie! pic.twitter.com/0ITaBdcjqs
— MalwareMustDie, NPO (@MalwareMustDie) September 29, 2014Operation "Chopsticks"
In this operation 29 hostile panels loaded with network attacker tools, ELF DDoS'er malware and windows malware, target IP list and botnet CNC tools was secured during the weekend & result was confirmed & evaluated in next Monday. The result we shared and reported as per below video:
MalwareMustDie!
...

 800+ IT
News
als RSS Feed abonnieren
800+ IT
News
als RSS Feed abonnieren